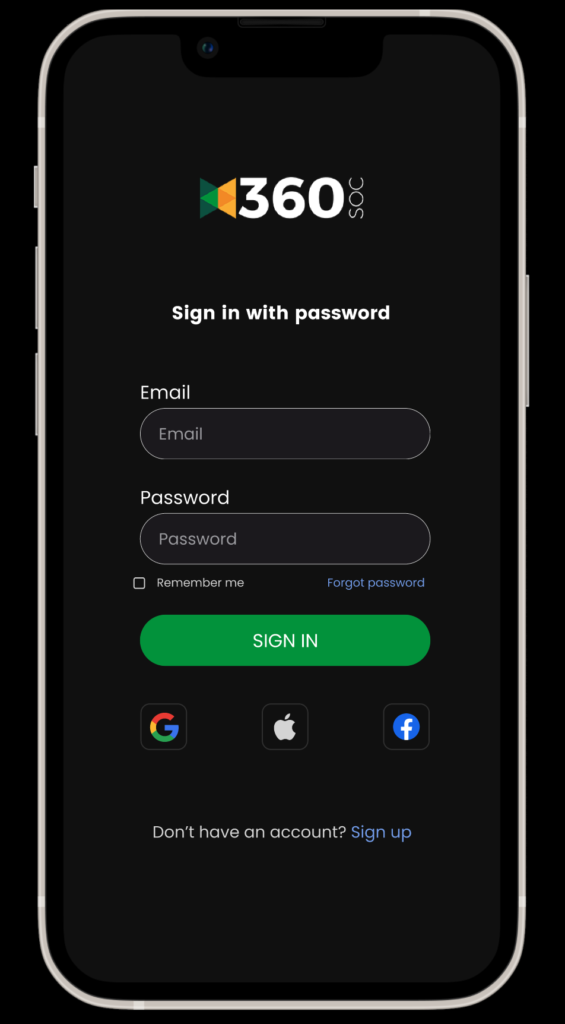
🚀 Exciting Announcement: Introducing 360 SOC’s Revolutionary and New SOC Platform with Mobile Access! 🚀
🚀 Exciting Announcement: Introducing 360 SOC’s Revolutionary and New SOC Platform with Mobile Access! 🚀 We are thrilled to announce the launch of our groundbreaking SOC Platform, bringing unparalleled convenience and security right to your fingertips! At 360 SOC, we continuously strive to redefine the user experience, and with this launch, we are truly …